This section provides a review of the academic and industry literature pertinent to the core components of this research: adversary emulation, Active Directory (AD) security, the role of threat intelligence, and the application of Multi-Criteria Decision-Making (MCDM) in cybersecurity. The aim is to contextualize the proposed framework and identify the specific research gap it addresses.
Adversary emulation: concepts, goals, and frameworks
Adversary emulation has emerged as a critical practice for proactively assessing and enhancing cybersecurity defenses against sophisticated threats like Advanced Persistent Threats (APTs)12. It involves simulating the Tactics, Techniques, and Procedures (TTPs) of real-world attackers to test detection capabilities, validate security controls, and train defenders2,10,13. The literature presents diverse approaches to conceptualizing and implementing adversary emulation, ranging from abstract simulations to automated execution frameworks and specialized documentation methodologies.
One stream of research focuses on simulating attacker behavior and network interactions. Drašar et al.11 introduced a session-level, event-driven simulator focused on analyzing attacker strategies and efforts based on varying entry points and credentials. This approach abstracts network interactions to the request-response level, offering insights into attacker progression but providing limited fidelity regarding specific operating system interactions or TTPs, particularly within complex environments like Active Directory (AD). While valuable for strategic analysis, its abstraction level distances it from the granular technique-level focus required for specific defense validation against known TTPs, such as those defined in the MITRE ATT&CK framework.
Moving towards more concrete TTP execution, several frameworks leverage the MITRE ATT&CK knowledge base, which has become a de facto standard for describing adversary behavior2,10,14. Karagiannis et al.14 proposed A-DEMO, a framework emphasizing the structured documentation of real-world cyberattacks (using a rootkit case study) by mapping attack phases directly to ATT&CK TTPs. The goal is to facilitate understanding, replication (emulation), and mitigation of documented attacks. While A-DEMO promotes standardized documentation and leverages ATT&CK effectively for describing known attack chains, it primarily focuses on replicating past incidents rather than proactively selecting or prioritizing techniques for specific environments or emerging threats. Its applicability to AD depends on the specific attack being documented.
Other approaches focus on automating the emulation process, often using ATT&CK as a library of executable actions. Applebaum et al.10 developed CALDERA, an influential automated adversary emulation system focused on post-compromise activities. CALDERA utilizes an automated planner built upon a logical encoding of the cyber environment and ATT&CK TTPs to intelligently select and execute actions to achieve predefined goals. This system is highly relevant to enterprise environments, often including AD, and its planning engine implicitly prioritizes actions based on goal achievement. Similarly, Ajmal et al.2 presented a threat-based adversary emulation approach, also leveraging ATT&CK, specifically for evaluating endpoint defenses in Windows environments. Their work emphasizes planning as part of the attack phase and includes algorithms for generating stealthy payloads, suggesting a prioritization based on effectiveness and evasion. Both CALDERA and the approach by Ajmal et al. represent significant steps towards automated, ATT&CK-driven emulation relevant to AD contexts. However, their prioritization mechanisms are either embedded within general planning logic10 or focused on payload generation and stealth13, rather than offering an explicit, configurable methodology for prioritizing techniques based specifically on the risks and characteristics of AD environments.
Addressing the challenge of realism and evasion, Orbinato et al. in13 introduced Laccolith, a hypervisor-based emulation solution designed for anti-detection. By injecting and executing malicious actions from below the guest operating system, Laccolith aims to bypass endpoint security controls (AV/EDR), thus providing a more realistic emulation of stealthy APTs. While capable of executing TTPs relevant to AD (e.g., credential dumping), its primary contribution lies in the evasion mechanism itself.
A distinct approach shifts the focus from individual TTPs or attack graphs to higher-level attacker objectives. Portase et al.9 proposed SpecRep, a system using a custom metalanguage derived from ATT&CK to define attack objectives. SpecRep compiles these objectives into multiple attack scenarios, exploring different combinations of actions (TTPs) to achieve the same goal. This objective-driven perspective inherently relates to prioritization, as achieving a specific objective (e.g., “Gain Domain Admin Access” in an AD context) requires selecting relevant TTPs. The system was demonstrated in heterogeneous infrastructures, including enterprise settings, but lacks a specific focus on AD intricacies or a dynamic prioritization mechanism beyond the initial objective definition.
In summary, existing research offers valuable frameworks and tools for adversary emulation, increasingly leveraging MITRE ATT&CK for structure and realism. Approaches range from high-level simulation11 and documentation14 to sophisticated automation2,10, objective-based planning9, and evasion techniques13. Several works2,10 are highly relevant to enterprise and AD environments and incorporate planning or threat-based selection, implicitly addressing technique prioritization. However, a specific gap exists in methodologies explicitly designed for prioritizing MITRE ATT&CK techniques based on the unique vulnerabilities, configurations, and high-value targets within Active Directory environments. Our work aims to address this gap by proposing a Data-Driven Approach for Prioritizing MITRE ATT&CK techniques leveraging Multi-Criteria Decision-Making (MCDM).
To clarify the distinctions and limitations across existing frameworks, Table 1 presents a comparative analysis of prior adversary emulation approaches, focusing on their primary objectives, integration of MITRE ATT&CK, applicability to Active Directory environments, and the presence or absence of explicit technique prioritization mechanisms.
Active directory security landscape
Recent CrowdStrike studies15,16,17,18 highlighted that adversaries are increasingly targeting identity-driven attacks, such as leaked account credentials, API keys, secrets, session cookies, tokens, one-time password (OTP) bypasses, and Kerberos-related vulnerabilities, including ticket manipulation. These attacks provide adversaries with the advantage of remaining stealthy and evading implemented defense mechanisms. Additionally, adversaries aim to minimize defenders’ network visibility by employing Living off the Land (LotL) binaries and therefore reducing potential indicators or alerts on the endpoint, which they recognize as being closely monitored. The studies also show that Kerberoasting attacks increased almost 600%. According to15,19 Active Directory (Domain Service) plays a crucial role for identity and access management in modern enterprises’ IT infrastructures, with 90% of Fortune 1000 companies relying on it. So, with the increasing number of identity-driven attacks and the reliance on Active Directory, once the adversary gains access to the system, they are poised to exploit this centralized infrastructure to escalate privileges, move laterally, and expand their control over the network. To increase persistence and bypass traditional detection methods, the attacker can use strategies such as Pass-the-Hash, or Silver Ticket. To gain control of sensitive corporate resources, they can also exert domain dominance by focusing on high-value accounts and group memberships. Since Active Directory is critical to an organization’s authentication and access control, compromising could have catastrophic effects that would allow APTs to achieve their goal.
For this reason, APT organizations target Active Directory to disrupt business operations, steal sensitive data or establish a persistent presence on an organization’s network. So, organizations should ensure that the Active Directory is adequately protected through strict monitoring, patch management and access controls to reduce the risk of attacks.
Strategies for mitigating APTs in active directory environments
Most research on APTs has been conducted from a reactive approach, where response mechanisms have focused on when a breach has already happened. These studies emphasize the detection and mitigation of attacks after adversaries have gained access to AD, which is often a critical point in the chain of compromises for APT groups. This section discusses how recent research has adopted a reactive approach to mitigate APT attacks.
A. Binduf et al.20 explored the AD environment, its structure and components. Additionally, they analyzed a case study of a hypothesis Saudi company that does not implement AD as an identity access manager (IAM), identifying significant security risks due to the lack of centralized control over user access and resources. Consequently, they analyzed the most common active directory security issues, such as Service Accounts has over-permissioned, A lot of Domain Admins, Using Group Policy Preferences (GPP) to handling credentials, and the use of weak passwords for local administrator accounts. They also highlighted the reactive approach by emphasizing the alert feature, which is designed to enhance accountability by notifying administrators when critical changes or events occur within the AD environment. Therefore, they emphasized that the major issue in many companies is the improper configuration or underutilization of this alert feature, leading to gaps in monitoring and delayed responses to suspicious activities. Authors in21 also explored Active Directory environment and determined the characteristics, and the potential security risk in the environment. They also utilized an AI-methodological assistant to automate the process of security assessment. Furthermore, this framework was a combination of using machine learning and graph-based methods. The paper highlighted the importance of vulnerability assessment and penetration testing (VAPT) and demonstrating the effectiveness of using AI.
For credentials dumping phase in APT lifecycle, Mohamed et al.22 concluded that traditional signature-based detection methods often fail to detect APT attacks due to their stealthy and evolving nature. Therefore, they proposed the Strange Behavior Inspection (SBI) Model that focuses on behavioral anomalies during the credential dumping, by monitoring suspicious behaviors in RAM, CPU, Windows registry, and file systems. As a result, the SBI model reduces the detection time from 9 months to 2.7 min with a 99.8% accuracy rate, providing a reactive defense mechanism against APT attacks.
Collectively, these studies highlighted a reactive paradigm in which security measures are implemented after attackers have gained access to the network, especially the Active Directory (AD) infrastructure, which is frequently targeted in APT campaigns because of its centralized function in access control and authentication. Each work contributes to a growing body of literature that prioritizes post-compromise detection and response strategies, rather than preemptive adversary disruption. From static signature-based detection models to more dynamic behavior-driven systems, such research highlights both the strengths and limitations of reactive approaches.
To better contextualize the value of our proposed approach, Table 2 contrasts existing works based on key dimensions including defense strategy (reactive vs. proactive), relevance to Active Directory (AD), degree of automation, presence of a proposed tool or framework, and whether TTP prioritization is supported. A closer examination reveals that the majority of existing research adopts a reactive strategy, where detection and response mechanisms are triggered after adversaries have gained access to AD environments. Works such as20,22,23,24 emphasize monitoring, alerting, behavioral analysis, or signature-based detection, often relying on historical footprints of APTs rather than disrupting the attack lifecycle proactively. While21 employs AI to assist in security posture evaluation, its proactive aspects remain limited to posture auditing rather than adversary emulation or threat-driven defense planning.
In contrast, our approach represents a proactive shift, leveraging automation and a decision-making engine to prioritize TTPs specific to AD environments before an attack occurs. Unlike prior works, our method introduces a data-driven, Multi-Criteria Decision-Making (MCDM) mechanism to explicitly prioritize MITRE ATT&CK techniques based on AD-specific risks, configurations, and asset sensitivity. This not only facilitates targeted emulation but also allows defenders to focus on the most relevant and impactful techniques for validation or hardening. The table underscores a clear gap in proactive, TTP-prioritized frameworks tailored to AD, a gap our work aims to fill thus illustrates its unique contribution in both strategy and operational applicability.
Role of threat intelligence in proactive security
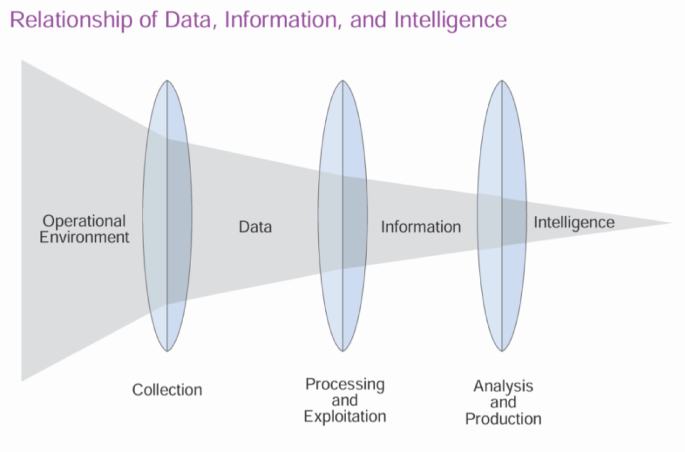
U.S. Department of Defense in26 demonstrates the relationship between data, information, and intelligence as a transformative process where raw data is processed into information, which is then analyzed to produce intelligence.
This relationship is illustrated in Fig. 1, which highlights how data evolves into actionable intelligence through various stages5. Authors in27 also, describe this process of Threat Intelligence as the process of moving topics from ‘unknown unknowns’ to ‘known unknowns’ by discovering the existence of threats and then shifting ‘known unknowns’ to ‘known knowns’, where the threat is well understood and mitigated.

Relationship of Data, Information, and Intelligence.
Furthermore, Cyber Threat Intelligence (CTI) is a critical component of modern cybersecurity strategy, providing organizations with the knowledge and foresight needed to anticipate, detect, and respond to cyber threats. CTI is broadly categorized into three main types: Strategic, Operational, and Tactical, each serving a distinct purpose within an organization’s security posture. These types are differentiated by their scope, time horizon, audience, and technical depth, and together they form a hierarchical model of threat-informed decision-making.
Strategic threat intelligence
Strategic Threat intelligence is high-level, long-term insights into the larger cyber threat landscape are provided by strategic threat intelligence. Executive decision-makers, including risk management executives, chief information security officers (CISOs), and chief technology officers (CTOs), are usually informed by it. This type of CTI focuses on the geopolitical or economic variables that drive cyber threats, the reasons for adversaries’ targeting of particular industries, and how new trends like AI weaponization and cyberwarfare will gradually change the threat landscape8,27.
Typically non-technical, strategic CTI can be found in government advisories, intelligence briefings, or white papers. Although it is not immediately actionable at the technical level, it directs the development of policies, the distribution of resources, and risk management plans.
Tactical threat intelligence
Tactical threat intelligence has a short-term focus and is quite detailed. Through the use of certain Indicators of Compromise (IoCs), such as malicious IP addresses, domain names, URLs, file hashes, email subjects, or known malware signatures, it focuses on the prompt identification and mitigation of attacks28. For real-time blocking and alerting, this intelligence is frequently immediately fed into Security Orchestration, Automation, and Response (SOAR) platforms or Security Information and Event Management (SIEM) systems.
For frontline defenders like SOC analysts, IT security managers, and network defenders, tactical CTI is essential, but it is frequently very reactive and lacks context. Although it is quite effective at thwarting existing threats, it becomes less useful when faced with new or developing attack methods that circumvent static signatures.
Technical threat intelligence
Technical Threat Intelligence is occasionally categorized alongside tactical intelligence; however, it is more precisely concentrated on low-level, machine-readable data utilized in automated detection and the formulation of signatures. This domain encompasses YARA rules, Snort signatures, Sigma rules, exemplars of exploit code, malware sandbox evaluations, and decompiled code segments5. The principal beneficiaries of this intelligence are malware analysts, reverse engineers, detection engineers, and architects of SOC automation. It furnishes the detection logic that underpins alerts and the forensic insights requisite for comprehensive analysis. Moreover, it facilitates the development of tools, the creation of correlation rules, and the enhancement of tactical and operational intelligence outputs.
Operational threat intelligence
Operational Threat Intelligence occupies a position that interlinks strategic and tactical intelligence regarding its breadth and technical intricacy. It furnishes mid-term, contextually rich perspectives on the operational methodologies of adversaries, particularly their tactics, techniques, and procedures (TTPs), tools, campaign behaviors, infrastructural utilization, and exploited vulnerabilities. Operational Cyber Threat Intelligence (CTI) is predominantly utilized by Security Operations Centers (SOCs), Cyber Threat Intelligence analysts, and Incident Response Teams (IRTs)8,27,28,29.
The significance of operational CTI resides in its capacity to effectively bridge the divide between intelligence and actionable measures. It underpins detection engineering, red/purple teaming, threat modeling, adversary emulation, and the formulation of incident response playbooks. It augments an organization’s capability to foresee the behaviors of attackers, construct defenses around recognized intrusion sets, and evaluate security systems against adversary TTPs aligned with frameworks such as MITRE ATT&CK.
Operational Cyber Threat Intelligence (CTI) holds significant importance in the realms of threat detection and forecasting. Through the examination of the historical and current activities of threat actors, cybersecurity professionals are equipped to identify recurring patterns, deduce probable vectors of attack, and emulate adversarial tactics. For instance, an awareness that an Advanced Persistent Threat (APT) group frequently employs Mimikatz for the purpose of credential extraction, or exploits a specific vulnerability to facilitate lateral movement, empowers defenders to proactively monitor these activities within their own operational environments.
In order to enhance the understanding of the distinctions and practical implementations of the three fundamental categories of Cyber Threat Intelligence; strategic, operational, and tactical, a systematic comparison is delineated in Table 3. This evaluation examines each type of intelligence in accordance with essential criteria, which encompasses its primary emphasis, temporal scope, data classifications, application scenarios, technical intricacy, relevant stakeholders, and inherent limitations. The intention is to elucidate their respective functions within cybersecurity operations, underscore their alignment with various decision-making tiers within an organization, and accentuate the unique benefits of operational threat intelligence in facilitating threat detection, adversary simulation, and the engineering of detection mechanisms.
Multi-criteria decision-making (MCDM) in cybersecurity
Multi-Criteria Decision-Making (MCDM) provides a structured framework for evaluating and prioritizing options in complex decision environments, such as cybersecurity, where multiple conflicting criteria must be balanced. In cybersecurity, MCDM is increasingly applied to optimize resource allocation, prioritize threats, and enhance incident response. This section reviews the application of MCDM in cybersecurity, focusing on its use in security controls selection, alert prioritization, and threat prioritization, with an emphasis on the novel contribution of prioritizing MITRE ATT&CK techniques. MCDM in cybersecurity typically involves defining criteria (e.g., risk, cost, impact, likelihood), assigning weights to reflect their relative importance, and using a decision-making method to rank alternatives. Common MCDM methods include the Analytic Hierarchy Process (AHP), Technique for Order of Preference by Similarity to Ideal Solution (TOPSIS), and Weighted Sum Model. These methods enable decision-makers to systematically evaluate options, ensuring optimal use of limited resources.
Yevseyeva et al.30 applied MCDM to the selection of security controls under budget constraints, modeling the problem as a two-stage process. In the first stage, managers determine the security budget, treating loss prevention as a gain. In the second stage, the budget is allocated to controls using a portfolio optimization approach, balancing two criteria: expected return (gain from loss prevention) and risk (covariance of controls). The Sharpe ratio is used to select the optimal control portfolio from the Pareto front, solved via quadratic programming. This approach leverages financial portfolio theory, emphasizing control diversity to minimize risk, but does not address specific threat frameworks like MITRE ATT&CK.
Bassey et al. in31 utilized an MCDM-like approach for prioritizing security alerts in Security Information and Event Management (SIEM) systems. Their sliding window algorithm computes a priority score based on three criteria: the severity of the current alert, the criticality of affected entities, and the severity of previous alerts for the same entities. By averaging these factors, the algorithm ensures that alerts impacting critical systems are prioritized, even if their severity is lower. While effective for alert triage, this method lacks a formal MCDM framework and does not consider structured threat models like MITRE ATT&CK.
Almeida and Respício in32 proposed a decision support framework for selecting information security controls, leveraging ISO/IEC 27,001 and 27,002 standards to map vulnerabilities to mitigative controls. Their approach employs an integer programming model to optimize security portfolios by minimizing both implementation costs and expected losses from vulnerabilities. The framework was implemented as an Excel-based tool, enabling managers to evaluate controls and simulate scenarios. While effective for cost-benefit analysis and compliance alignment, the method relies heavily on predefined standards and does not incorporate dynamic threat intelligence or advanced multi-criteria decision-making (MCDM) techniques for evolving cyber threats.
In33 authors proposed a sector-based threat profiling approach for security control prioritization, leveraging MITRE ATT&CK and ETDA Threat Group Cards to map active threat actors’ TTPs to controls from ISO 27,001, NIST SP 800 − 53, and CIS frameworks. The methodology weights actors based on operation recency and newness, then prioritizes controls by their coverage of high-risk TTPs. While the approach automates threat-informed decision-making, it relies heavily on third-party data sources and lacks granularity in control effectiveness metrics. Unlike traditional vulnerability-centric models, this outside-in method aligns defenses with real-world adversary behaviors but may overlook organization-specific risks.
In contrast, the proposed research introduces a novel MCDM-based approach for prioritizing MITRE ATT&CK techniques, addressing a gap in structured threat prioritization. By selecting criteria such as threat impact, Prevalence, detection difficulty, and applying an MCDM method, the approach generates a ranked list of MITRE techniques tailored to an organization’s context. This enables targeted resource allocation and incident response, enhancing cybersecurity resilience. Unlike30,33, which focuses on control selection, or31, which addresses alert prioritization, this work directly tackles threat prioritization, leveraging the MITRE ATT&CK framework to provide actionable insights for defenders.
Our work proposes an MCDM-based approach to prioritize MITRE ATT&CK techniques for adversary emulation, using multiple criteria leveraging threat intelligence. It addresses inefficient, untargeted emulation by focusing on relevant threats, enhancing resource efficiency and tailoring defenses to organizational risks, thus strengthening resilience against advanced persistent threats (APTs).
The criteria adopted in this study significantly diverge from those employed in prior MCDM-based cybersecurity applications by emphasizing a threat-centric and adversary-informed perspective tailored to the context of adversary emulation. Previous works, such as30,32, largely focused on criteria related to static factors, implementation cost, compliance requirements, or control availability, framing security decision-making primarily around risk management or budget optimization. While effective in general control selection, such approaches often lack responsiveness to the dynamic and evolving nature of threat actor behavior.
In contrast, our study introduces a novel set of criteria specifically selected to enhance the fidelity and relevance of emulating real-world adversarial techniques, particularly in Active Directory environments. These criteria are aligned with both threat intelligence and operational feasibility, ensuring that the resulting prioritization supports proactive security testing and incident response preparation.
By framing criteria selection around both attacker intent and defensive capability, this approach improves upon prior MCDM applications by offering a dynamic, context-aware, and attack-surface-specific prioritization framework. This distinction is particularly critical for adversary emulation, where selecting techniques without considering attacker likelihood or detection challenges may lead to ineffective or unrealistic simulations. As such, the proposed criteria represent a substantial advancement over traditional MCDM configurations, aligning decision-making more closely with the realities of threat-informed defense.
In this study, entropy-based weighting is employed as the preferred method for determining the relative importance of decision criteria due to its objective, data-driven foundation and its alignment with the dynamic nature of threat intelligence-informed prioritization. In contrast to subjective weighting techniques, such as pairwise comparison matrices used in the Analytic Hierarchy Process (AHP) or expert-assigned static weights. Entropy-based weighting derives criterion importance directly from the inherent variability of the data. Specifically, it quantifies the degree of information dispersion (entropy) across alternatives, thereby assigning greater weight to criteria that provide higher discriminative power in the decision matrix.
This attribute is particularly advantageous in cybersecurity contexts, where the salience and influence of evaluation criteria can fluctuate based on evolving adversary behaviors, shifting threat landscapes, and organizational-specific vulnerabilities. By allowing the weighting to adapt automatically to data variability, the entropy method enhances the contextual relevance of the prioritization outcome without requiring manual tuning or subjective input.
Furthermore, the entropy approach contributes to methodological robustness by promoting scalability, reproducibility, and transparency, key requirements in empirical cybersecurity research. As the proposed approach is intended to support an automated and adaptable framework for the prioritization of MITRE ATT&CK techniques, entropy-based weighting ensures that the decision-making process remains unbiased, responsive to data changes, and grounded in quantitative analysis. Consequently, this methodological choice strengthens both the scientific validity and practical utility of the prioritization framework.
link