Cyber expert shares top 10 social engineering techniques | Analysis

Social engineering attacks use human nature to their advantage, preying on our trust, greed, fear, curiosity, and even our desire to help others.
A recent study found that 75% of respondents believe that social engineering and phishing attacks are the biggest danger to cybersecurity at their company.
Cybersecurity threats are evolving, and while the incidence of traditional attacks may decrease, more sophisticated ones will prosper. Staying alert and being educated are the keys to staying safe.
Carlos Salas, an engineering manager at NordLayer, shares 10 social engineering techniques that hackers may use to target both individuals and organisations.
According to Salas, “Social engineering is one of the easiest ways to get access to sensitive data, especially when employees haven’t been trained on how to recognise and combat it. Because every member of the organisation is a potential target, with interactive and informative training, such attacks can be stopped.”
- Baiting
Baiting attacks use a false promise to rouse a victim’s greed or curiosity. Social engineers use bait to lure users into a trap that steals their personal information or infects their systems with malware. For example, infected USB memory sticks are left in parking lots or offices, tempting people to see what’s on them. Don’t ever try to check what is inside the unattended USB devices, and make sure to report it to the security team if you see them lying around.
- Pretexting
An attacker uses a made-up scenario (a pretext) to provoke an employee to disclose sensitive information, for example, login details to IT systems or personal information about other employees. It often requires researching the target prior to the attack to make the scenario plausible and to gain the trust of the victim. If that happens, the most important thing is to verify the identity, avoid sharing personal details and report the incident to the IT team.
- Watering hole
In a watering-hole attack, the attacker infects an existing website or creates a fake website that mimics an existing website often used by a certain group of people, for example, employees of a company. The goal is to infect a targeted user’s computer and gain access, for instance, to the network at the target’s workplace. To protect yourself, only access websites that have HTTPS in the URL code, update your software, and use malware-detection tools.
- Quid pro quo
Quid pro quo attacks rely on people’s sense of reciprocity. Attackers offer services, assistance, or other benefits in exchange for information. For example, someone pretending to be an IT expert might ask for your device’s login credentials in order to make that device run faster. In order to prevent information loss, verify the identity of IT technician, question methods and tools, and use anti-malware software.
- Scareware
Scareware is a form of malicious software, usually a pop-up that warns that your security software is out of date or that malicious software has been detected on your machine. It fools victims into visiting malicious websites or buying worthless antivirus software. Use an ad-blocker and reputable antivirus and avoid clicking on pop-ups.
- Tailgating and piggybacking
Tailgating and piggybacking involve an attacker accessing a secure or restricted area. For instance, a person might tailgate an employee into the office, claiming to have lost their access card, pretending to be a repair technician, or holding coffee cups in both of their hands and asking for your help with the door.
- Vishing
Vishing, also known as “voice phishing,” is a practice of eliciting information or attempting to influence someone via the telephone. Avoid responding to emails or social media messages that ask for your phone number. Remember that your colleagues will never call you at home asking you to transfer funds or any other sensitive information.
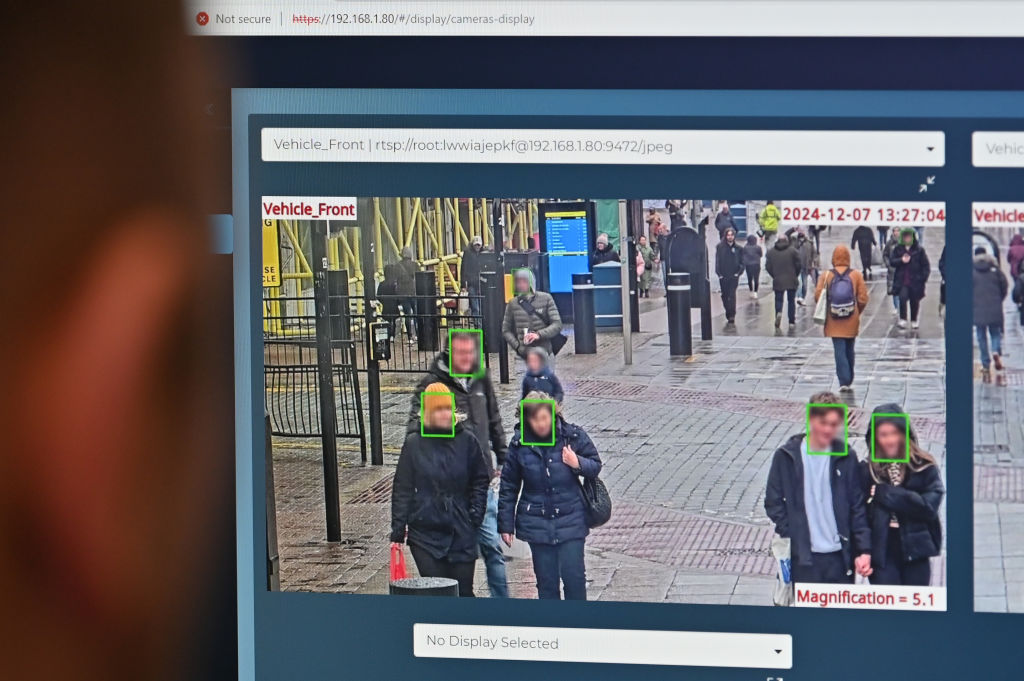
- Shoulder surfing
Shoulder surfing is the bad actor watching their unsuspecting victim while they’re entering passwords and other sensitive information. But this technique doesn’t have to be used at close range, literally looking over their shoulder. It could be employed by the hacker from a distance if they use binoculars or hidden cameras, for example. In order to eliminate the risk of being snooped on this way, make sure to use strong, single sign-on passwords, biometrics, and 2-factor authentication.
- Dumpster diving
Dumpster diving is when attackers go through your company’s rubbish looking for documents containing sensitive or confidential information. Always use a file shredder to prevent information leakage.
- Deep Fakes
Deepfakes (“deep learning” + “fake”) are synthetic media in which a person in an existing image, audio, or video is replaced with someone else’s likeness. It is possible to detect deep fakes. Make sure to check for shadows appearing on the face, notice if eyes are blinking and try to detect wrinkles. Beware of poor-quality phone call recordings and pay attention to how letters like f, s, v, and z are pronounced — software has trouble differentiating them from noise.
link