How To Mitigate Risk In Shared Login Environments

Michael Engle is Cofounder at 1Kosmos and was previously head of InfoSec at Lehman Brothers and Cofounder of Bastille Networks.
Who hasn’t shared non-sensitive login credentials, like an online shopping account, with a family member or friend? While harmless in personal settings, it’s well understood that shared credentials in business environments pose a serious security risk. Nevertheless, shared accounts remain a common practice in many workplaces.
Consider factory floors, call centers, retail fulfillment centers and hospitality services. In these environments, shared logins are a fact of life and represent an attack surface ripe with vulnerability. Shared accounts are frequently utilized to grant multiple users access to a single workstation or application.
However, traditional management methods, such as generic passwords or physical tokens, are vulnerable to compromise. The use of shared credentials makes it impossible to attribute actions to specific individuals, thereby increasing the risk of security breaches, non-compliance and potential misuse within organizations.
While more secure than shared passwords, physical tokens introduce their own challenges. Tokens can be lost, damaged or forgotten, causing disruptions to operations. They also impose significant costs in large-scale deployments, particularly in high-turnover environments.
Modern authentication methods provide a better approach to shared login security by eliminating shared passwords while enabling secure, efficient and user-friendly access to resources and applications.
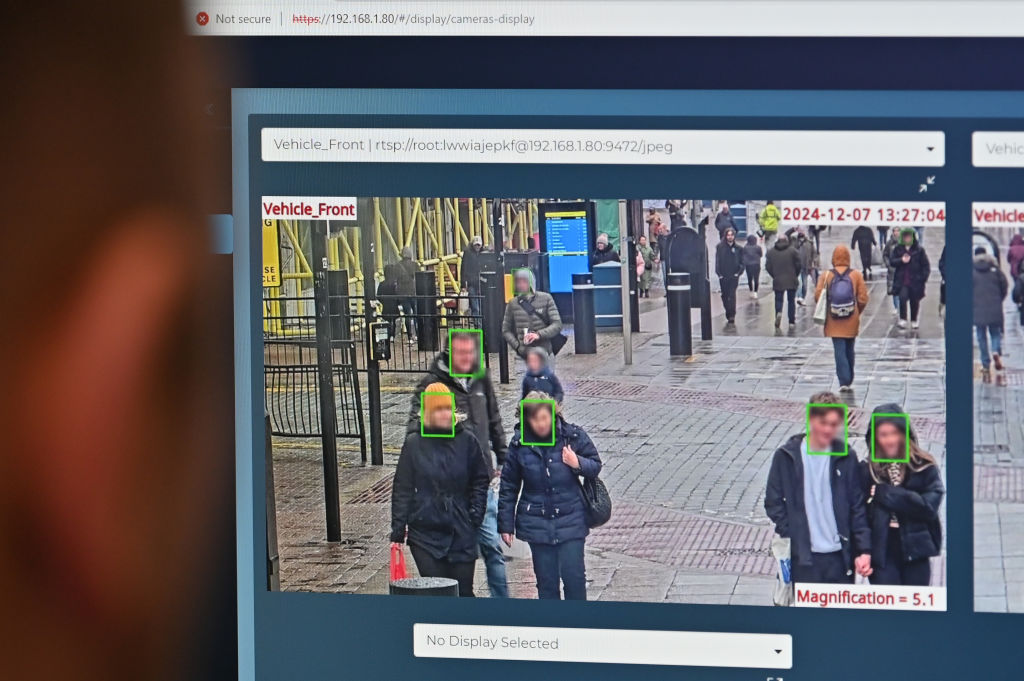
Biometrics
Biometric-based authentication provides a solution for managing shared logins. Using FIDO-compliant biometric keys with “register once, use on any device” functionality, organizations can enable secure, password-free authentication without needing physical tokens. Employees can enroll their biometrics once and easily access multiple workstations or applications, reducing friction and boosting productivity.
This approach not only simplifies access but also ties every login event to an individual user, creating a secure, auditable trail. This capability addresses critical security and compliance needs while improving accountability in shared environments.
Here are some examples of how biometric authentication for shared login can improve operational efficiency and security in various industries:
• Manufacturing: On factory floors, shared accounts are frequently used for workstations that monitor equipment or order parts. Generic credentials like “factory/factory” compromise security and obscure individual accountability. Biometric authentication bridges this gap by converting a user’s fingerprint into the shared credential required by the system. This ensures security while maintaining operational workflows.
• Call Centers: High-security settings often restrict the use of personal devices to protect sensitive customer data. Shared logins, however, introduce risks such as credential misuse and unauthorized access. Biometric authentication can secure individualized access to shared systems, enhancing both security and efficiency.
• Retail Fulfillment Centers: Time is critical in fulfillment warehouses, where employees log in to shared systems to track orders or manage inventory. Typing credentials wastes valuable seconds, impacting overall productivity. Biometrics eliminates this friction while securing access.
• Hospitality And Maritime: Shared login systems are widely used in hospitality and on ships, where multiple employees interact with critical systems. Without secure authentication, these environments face heightened risks of credential misuse and data breaches. Biometrics ensures every access is secure, auditable and user-specific.
Lower Cost And Better Scalability
Workstation-based biometric authentication offers a scalable alternative to physical security tokens. Unlike solutions like Windows Hello and Apple Touch ID, which may require per-device enrollment and have user limits, a single workstation can authenticate multiple users through biometrics. This approach reduces costs and complexity, especially in organizations with high turnover or large, diverse workforces.
Privacy protection is achievable through advanced encryption and distributed system architecture. By decentralizing biometric data storage while keeping private keys under user control, organizations can better prevent large-scale breaches while meeting strict privacy requirements.
Best Practices For Biometric Shared Login
My key implementation recommendations include:
1. FIDO Standards: Deploy FIDO-compliant systems to ensure interoperability and prevent credential theft.
2. Infrastructure Integration: Select solutions compatible with privileged access management (PAM) platforms and IT systems for efficient shared credential management.
3. Individual Accountability: Link all access events to specific users for audit trails.
4. Scalable Deployment: Install fixed endpoint devices supporting multiple users to reduce costs and management complexity.
5. Privacy Protection: Implement encrypted, privacy-preserving designs that protect biometric data and maintain regulatory compliance.
Adopting biometric authentication isn’t just a technological upgrade; it’s a fundamental shift in how organizations approach security and operational efficiency in shared login environments. It enables organizations to protect sensitive systems, meet regulatory requirements and establish a productive work environment where every access is secure, accountable and traceable.
Forbes Technology Council is an invitation-only community for world-class CIOs, CTOs and technology executives. Do I qualify?
link