Modern cybersecurity techniques that you didn’t know about

Keeping up with cutting-edge cybersecurity methods is no longer a luxury in this age of unprecedented digital threat evolution; it is an absolute need. In this article, we will explore some of the most innovative methods now used to safeguard digital assets.
From leveraging artificial intelligence to adopting quantum encryption, these methods showcase the future of cybersecurity. Particularly, online casinos such as Raja567, which handle vast amounts of sensitive financial data, are adopting these advanced security measures to protect against cyberattacks and ensure customer trust.
As these gambling platforms increasingly operate online, the application of sophisticated cybersecurity techniques becomes critical in safeguarding both the operators and their users.
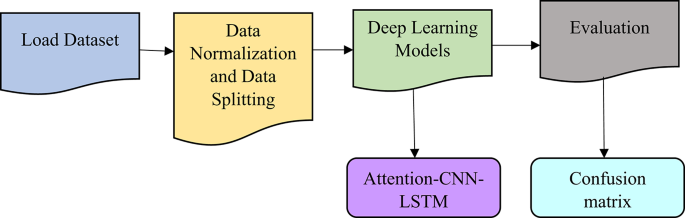
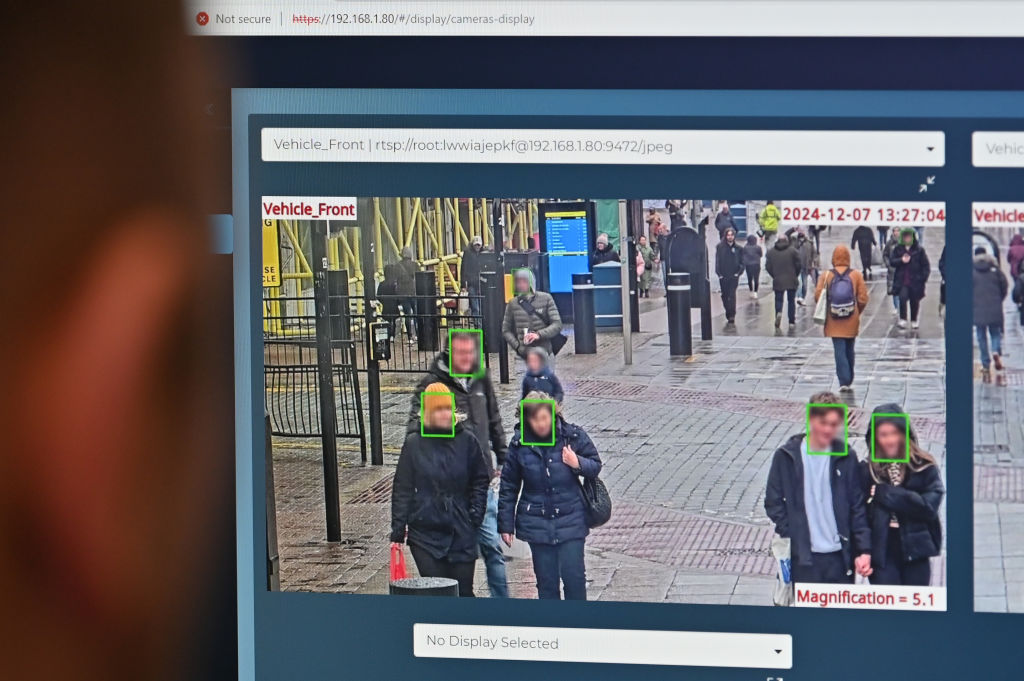
Behavioural analytics
Behavioral analytics in cybersecurity is realised through sophisticated programs that use machine learning to detect unusual activities. Here are some notable tools:
- Splunk User Behaviour Analytics: Analyses user activity to identify anomalies like unusual access patterns that could suggest a breach.
- Exabeam Advanced Analytics: Builds smart timelines of security events across devices, identifying deviations from normal behaviour that could indicate threats.
- Aruba IntroSpect: Uses AI to learn typical user behaviours on the network, helping to pinpoint unusual activities.
- Rapid7 InsightIDR: Combines SIEM, UBA, and EDR to monitor for suspicious behaviour across users and devices.
- Darktrace: Models a ‘pattern of life’ for network entities, instantly spotting and responding to deviations.
Imagine you’re working from a cafe, and suddenly you’re accessing the corporate financial records at 3 AM—a time you’re usually asleep. A tool like Exabeam might flag this activity, sending an alert that perhaps a night owl hacker, and not you, is prowling through the financials while everyone else is dreaming of spreadsheets.
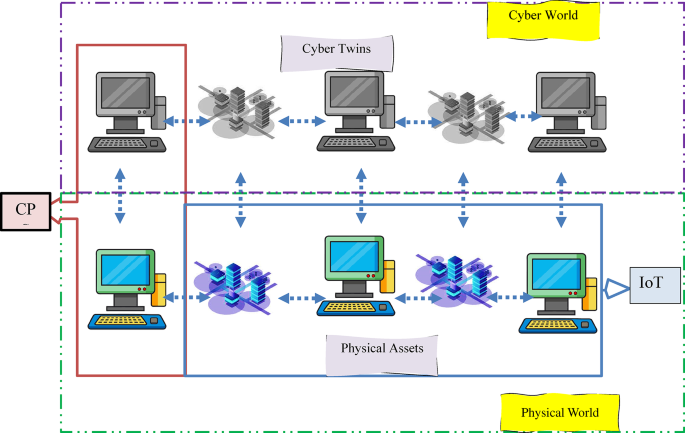
Zero Trust Architecture
Zero Trust Architecture takes the “trust no one, question everything” approach to cybersecurity, implementing a rigorous “never trust, always verify” regime. Here’s how this rather paranoid security strategy works:
- User Authentication: Every user must prove their identity through robust authentication methods before accessing any network resources.
- Device Security Posture Check: Only devices meeting strict security compliance can access the network.
- Least Privilege Access Control: Access rights are minimised to what’s absolutely necessary for each task.
- Microsegmentation: The network is divided into secure segments to limit potential lateral movement by attackers.
- Continuous Monitoring: Just assume you’re always being watched, because, well, you are. It’s for your own digital safety, of course!
So, if you’re running an online casino, implementing Zero Trust is like hiring the world’s most overzealous bouncer. Sure, it might slow down the fun a bit, but at least you know the only one rolling the dice is someone who’s supposed to be there.
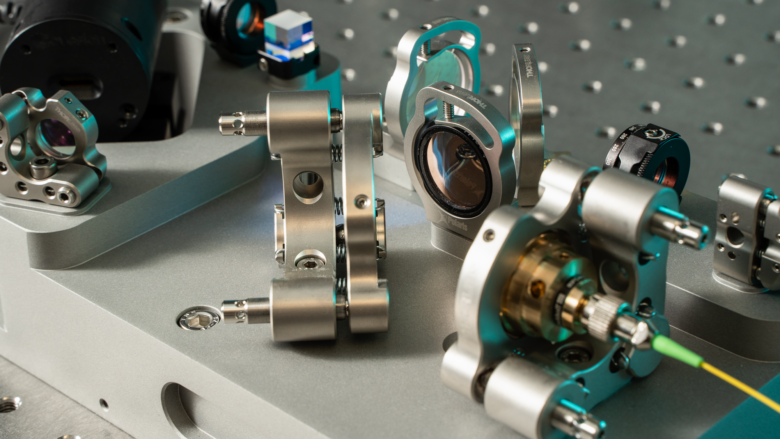
Quantum Cryptography
Quantum Cryptography leverages the quirky world of quantum mechanics to ramp up data security, using Quantum Key Distribution or QKD that’s about as easy to intercept as catching a greased pig in a dark room. The following table summarizes the key points of QKD:
| Aspect | Description |
| Principle | Uses quantum mechanics to transmit keys securely. |
| How It Works | Sends cryptographic keys using photons; any tampering changes their state, alerting both sender and receiver. |
| Security | Alerts both parties instantly if there’s eavesdropping, because surprises are only fun at parties, not in data transmission. |
| Use Cases | Mainly in government and finance sectors, with potential for broader use as technology advances. |
| Future Outlook | Expected to become more common as a defense against conventional cyber threats as quantum tech evolves. |
To bring it home, imagine you’re texting your friend about your surprise party plans for another friend. With quantum cryptography, if someone sneaky tries to read those texts, it’s like the words scramble themselves into a jumbled mess. Only your friend, with the right quantum key, gets the message clear as day—ensuring the surprise isn’t ruined by nosy onlookers.
Automated Security Platforms
In the realm of cybersecurity, automated security platforms serve as superheroes, each with their own special set of abilities to safeguard the digital cosmos. Some notable tech guardians and the superpowers they possess are summarized here:
- Super Power: With the reflexes of a ninja, this platform scans billions of events per day, using AI to detect and respond to threats faster than a speeding bullet.
- IBM QRadar: Armed with the wisdom of a sage, it combines the traditional strengths of SIEM with advanced AI, making sense of mountains of data to sniff out threats and keep compliance on track.
- Palo Alto Networks Cortex: Think of it as the omnipresent eye, offering AI-driven security insights across every corner of your network, whether on-premises or in the cloud, automating tasks and slashing response times.
- Cisco SecureX: This is the team player of security tools, integrating data across all Cisco products to provide a unified defense strategy that automates responses and bolsters your security lineup.
- Darktrace Antigena: Mirroring the human immune system, this AI-driven protector learns what’s normal for your network and autonomously responds to anomalies, all in real time.
As AI in cybersecurity evolves, expect less cyber-battlefield and more preemptive peacekeeping. Imagine a future where security systems not only thwart attacks but predict them, giving hackers a metaphorical “I wouldn’t do that if I were you” warning.
We might even see our fridges collaborating with firewalls, protecting our digital and dietary choices alike. “Sorry, Dave, no expired yogurt or phishing scams today!” With AI doing the heavy lifting, managing cybersecurity could become as routine as household chores.
Conclusion
In conclusion, while we’ve touched on a handful of clever systems here, there are countless more shrouded in mystery—undoubtedly tucked away in some top-secret government bunker or hidden in the Masons’ latest newsletter. Who knows what high-tech wizardry they’re keeping under wraps? Rest assured, the layers of cybersecurity intrigue run deep and dark!
Sponsored
link