Offensive cyber security training for professionals
As the cyber threat landscape continues to evolve, organizations need cyber security professionals with cutting-edge offensive skills. LRQA’s Offensive Cyber security Training empowers individuals to understand and exploit weaknesses in corporate networks, simulating real-world cyberattacks. Our training covers the latest red teaming techniques, penetration testing methodologies, and ethical hacking tools, ensuring that participants are well-prepared to counter cyber threats.
Through a mix of theoretical knowledge and hands-on lab-based exercizes, learners are immersed in an environment that mirrors corporate networks. This allows them to apply offensive cyber security techniques in realistic scenarios, improving their ability to detect and mitigate vulnerabilities. Our training aligns with industry-recognized standards and is delivered by seasoned experts with extensive red teaming experience.
Award-winning expertise
Our cyber security team continues to achieve multiple vendor certifications, highly respected industry accreditations and international accolades, demonstrating the breadth, depth and impact of their services.
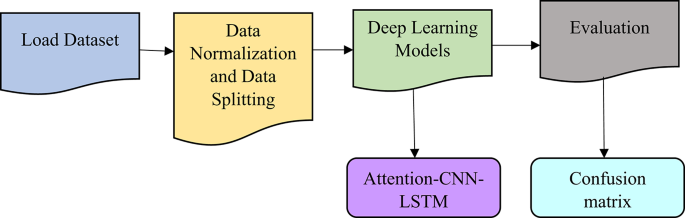
 The latest techniques
The latest techniques
The latest techniques, tactics and procedures (TTPs) being used by real-world threat actors will be demonstrated on a practical level. This includes stealthily bypassing defensive security controls (Common EDRs and next-gen AV), which are typically operating within modern enterprise environments.
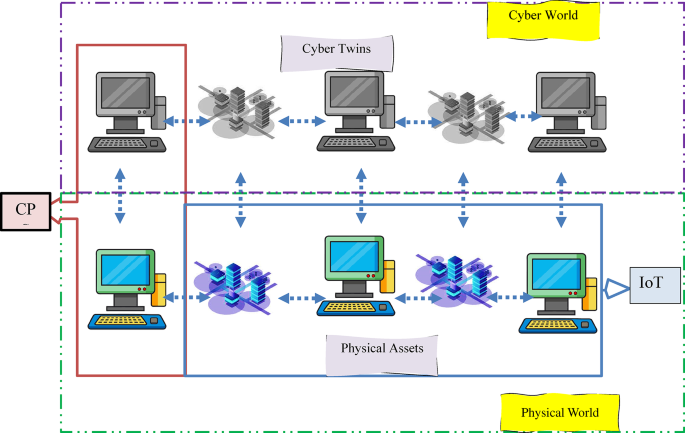
 Replication of corporate networks
Replication of corporate networks
Includes both a theory element as well as hands-on practical exercises, where the techniques learned can be practiced in a training lab environment specifically designed to replicate a typical corporate network.
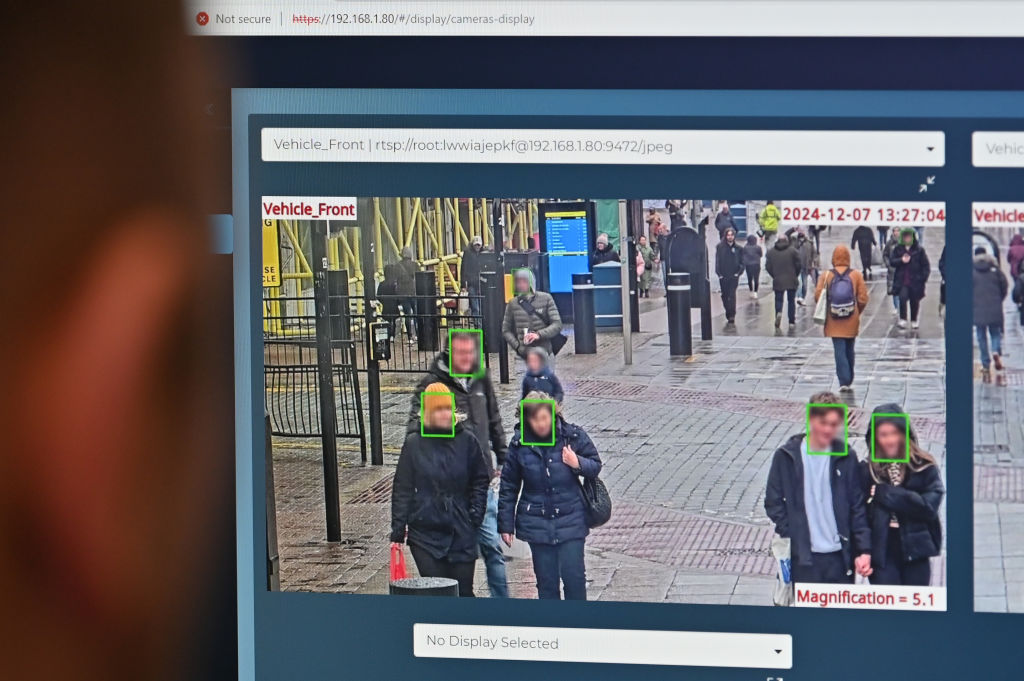
 Blue Teaming included
Blue Teaming included
Our training also covers common defensive techniques that are deployed by the blue team, such as host-based event logging and monitoring, strict egress filtering, application whitelisting and various other endpoint protections.
 Expert guidance
Expert guidance
Enumerate the target objective and attempt to compromise the critical system in scope for the Red Team. This will include multiple levels of privilege escalation and lateral movement to gain access to the objective system.
The world leader in CREST accreditations
We are proud to be the only organization in the world with a full suite of accreditations from The Council of Registered Ethical Security Testers (CREST).
Our team of consultants have achieved the highest accreditations for Penetration Testing, Red Teaming, Incident Response services and Threat Intelligence. In addition, we were also the first organization to be CREST accredited for our Security Operation Centre services.
Make an inquiry or request a quote
Protect your organization with LRQA’s award-winning cyber security services. Please complete the form below and we will get back to you.
link